|
'study/ccna'에 해당되는 글 8건
[Schizo!, 2008. 11. 22. 22:38, study/ccna]
ccna 2 final Why would an administrator change the value highlighted in the exhibit? (Choose two.) -to make the router bypass the startup-configuration file -to configure the router to boot the RXBOOT image During initial router bootup the following line appears: -The router has not been configured. -The startup-config file cannot be located. A new technician must add boot system commands to one of the department routers. Which available commands will the router return as output when the command shown below is entered? (Choose two.) -TFTP -FLASH What information can be learned during the initial router bootup? (Choose two.) -the number and types of interfaces installed -the router model and the amount of memory that is available Which of the following are primary functions of a router? (Choose two.) -packet switching -Path selection
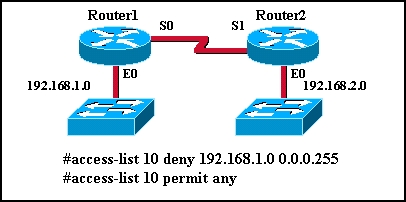
-Montgomery has Layer 2 connectivity with Cumberland. -Brant, Fisherman, and Potomac are directly connected to Montgomery. Which router components and operations are correctly described? (Choose two.) NVRAM - stores the configuration file POST - runs diagnostics on hardware modules What are the results of setting the boot field bits in the configuration register to "0000"? (Choose two.) -The router will enter ROM monitor mode upon reload. Which commands will correctly configure an extended ACL? (Choose two.) -Router(config)# access-list 192 permit icmp host 198.18.4.3 172.22.0.255 0.0.0.0 echo -Router(config)# access-list 153 deny udp 10.43.0.0 0.0.255.255 any eq 161 Which commands will show the status and IP address of all interfaces on a router? (Choose two.) -show protocols -show interfaces An administrator needs to determine if RIP v1 or IGRP should be used in a small network. Which two statements are true and should be considered by the administrator before making the decision? (Choose two.) -IGRP will use the available bandwidth and calculated traffic delays on the link to help determine the best path. -IGRP can be implemented on large networks up to 255 hops in diameter. Which of the following statements are true regarding routed protocols? (Choose two.) -They provide enough information in the Layer 3 address to allow a packet to be forwarded from one network to another. -They carry user data between networks. Which two steps describe how to create a functional physical connection between a router console and a terminal? (Choose two.) -Use an RJ-45 to DB-9 adapter on the terminal serial port to connect to the cable going to the router console. -Use a rollover cable to connect from a terminal serial port to the router console port. What are two possible reasons a router would not load a valid IOS from flash? (Choose two.) -The first boot system command executed in the startup configuration file is boot system rom. -The configuration register is set to 0x2100. access-list 199 deny tcp 198.18.0.0 0.0.255.255 any eq 25 -SMTP traffic from hosts on network 198.18.0.0 will be denied. -SMTP and HTTP traffic to hosts on the 198.18.0.0 network is permitted.
-This is a named extended ACL that allows any host on 192.168.85.0 to Telnet to address 172.25.0.26. -All FTP and HTTP traffic destined for 172.25.0.26 will be denied.
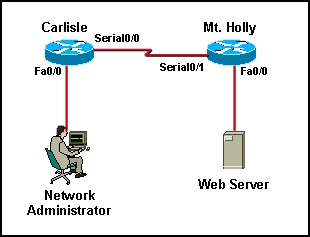
-ATL# 192.168.4.2 -CHI# telnet 192.168.4.1 From the running-config, the following configuration entries are displayed: -Three Telnet lines are available for remote access. -Remote access to this local router will require a Telnet password of g8k33pr. What are two characteristics of the support for Telnet within Cisco IOS software? (Choose two.) -Up to five separate Telnet lines are supported by default in standard edition IOS files. -A router can host simultaneous Telnet sessions. What are two recommended uses of login banners? (Choose two.) -to display security warning messages -to announce a scheduled system shutdown Which features describe a FastEthernet interface on a router? (Choose two.) -may be administratively disabled by using the shutdown command -must be configured with a valid IP address and subnet mask in order to forward packets What will occur if the command service password-encryption is entered on a router? (Choose two). -It will apply a weak encryption to all unencrypted passwords. -It will configure the user EXEC mode, telnet, and enable passwords as encrypted. Choose 3 Which procedures will work while configuring the router using the setup configuration utility? (Choose three.) -Press Enter or the Return key to accept the default values. -Enter the address on an interface or add a new routing protocol suite. -Press Ctrl-C to return to the privileged mode prompt or to terminate setup mode.
-modem -DCE device -CSU/DSU
-Marketing(config)# ip route 0.0.0.0 0.0.0.0 fa0/0 -Sales(config)# ip route 192.0.2.0 255.255.255.0 fa0/0 -Sales(config)# ip route 0.0.0.0 0.0.0.0 s0/0
-The version for this IOS file is 12.1 release 5. -Where the file is stored on the router and whether the file is relocatable is indicated by the expression mz. -This image could be used on a 2621 or a 2620 with enough RAM. What are three features of CDP? (Choose three.) -provides information on directly connected devices that have CDP enabled -tests Layer 2 connectivity -enabled by default on each interface The following access list has been correctly applied to a router interface: -A wildcard mask of 0.0.0.0 is assumed for 172.30.65.52. -All traffic from 172.30.65.51 will be permitted. -This is a standard IP access list. Why are interface descriptions used in router configurations? (Choose three). -to enable support personnel to easily identify networks and customers that may be affected by a possible interface issue -to provide comments on the interface without affecting the router functionality -to identify the purpose and location of the interface Single answer In what order will the initial startup routine of a router locate and load the IOS if the config-register setting is 0x2102 and there are no boot system commands present in the startup-config file? -Flash, TFTP server, ROM
-Networks 198.18.100.0/24 and 172.23.0.0/16 will be unreachable from Marshall and Fiji.
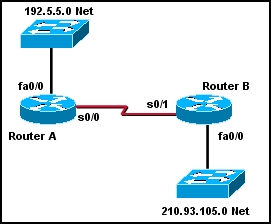
-The ip classless command is not enabled on Router A.
-B(config)# router rip Which router component stores the information that is displayed by the show arp command? -RAM If a PC does not have network connectivity to a router, which router port can be used to establish communication? -Console What can a network administrator do to recover from a lost router password? -boot the router to ROM monitor mode and configure the router to ignore NVRAM when it initializes
-Tokyo(config)# interface fa0/0 A network administrator must configure a FastEthernet interface with an IP address. The configuration must also identify the remote site to which the interface is connected. Which set of commands will meet these requirements? -StPetersburg(config)# interface fa0/0 A network administrator issues the erase startup-config command on a configured router with the configuration register set to 0x2102 and observes the following output: -The router will prompt the user to enter setup mode or to continue without entering setup mode. The main router of XYZ company has enough flash and RAM to store multiple IOS images. An administrator wants to upload a second IOS image from a TFTP server to the flash of the router. Which method will accomplish this task? -Copy the IOS image file from a TFTP server using the command copy tftp flash. When prompted, provide the IP address or name of the TFTP server and the IOS image filename.
-ROM
-access-list 33 deny 172.16.34.0 0.0.0.255
-5 seconds
-WinterPark(config)# ip route 0.0.0.0 0.0.0.0 192.168.146.1
-access-list 125 permit ip 192.168.2.0 0.0.0.255 any
-The Finance Admin host and the HR Admin host will be able to ping to each other. The HR Admin host will be allowed to access Web servers on the Internet, while the Finance Admin host will be denied Internet Web access.
-Use the show interfaces command from a Telnet session on router B to check the connection to router C.
-A, B, D, E, F What can be determined from this output? -57625 is a composite metric used by IGRP in calculating the best path. 'study > ccna' 카테고리의 다른 글
[Schizo!, 2008. 11. 8. 12:57, study/ccna]
1 Which statements are true regarding the significance of the access control list wildcard mask 0.0.0.7? (Choose two.) 8 • Router1# configure terminal Router(config)# access-list 2 deny 172.16.5.24 What can be concluded about this set of commands? 15 Which statement is true regarding wildcard masks? 17 Which of the following matches an ACL identification number with the correct protocol?(Choose three.) 'study > ccna' 카테고리의 다른 글
[Schizo!, 2008. 10. 28. 09:15, study/ccna]
1 Which of the following describe how TCP adds reliability to communication? (Choose three.) 2 A computer programmer is developing software that requires a reliable stream of data. Which protocol can be used in the software design to eliminate the need for building error detection and recovery into the application program? 3 Why is TCP considered a connection-oriented protocol? 6 How are originating source port numbers assigned during the data encapsulation process? 7 Which of the following would an administrator do to defend against a denial of service SYN flooding attack? (Choose two.) 8 When a host receives a data segment, what allows the host to determine which application should receive the segment? 11 In the TCP header, which of the following determines the amount of data that can be sent before receiving an acknowledgment? 13 Which of the following protocols uses UDP for transport layer services? 14 What type of segment and data is shown in the graphic? 15 What is the purpose of Positive Acknowledgment and Retransmission (PAR)? 16 Which of the following are functions of the TCP protocol? (Choose three.) 17 What is used by both TCP and UDP when creating a segment? 18 Which authority has control over the assignment of port numbers for applications? 19 Which of the following describe types of port numbers that can be represented in the headers of TCP and UDP segments? (Choose three.) 20 What is the purpose of the three-way handshake that occurs between hosts using TCP as the transport layer protocol? 21 During the encapsulation process, in which order are the IP address, MAC address, and port number assigned when the router is establishing communication with the TFTP server? 23 Which transport layer unit of information places the port number in the header? 'study > ccna' 카테고리의 다른 글
[Schizo!, 2008. 10. 28. 09:11, study/ccna]
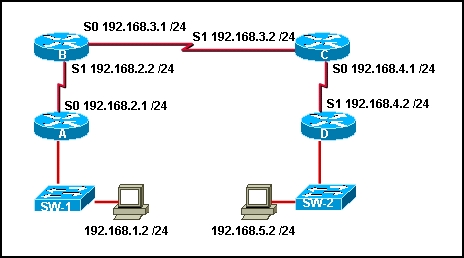
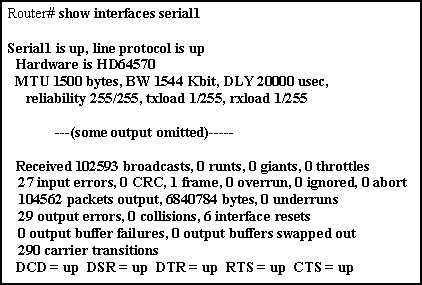
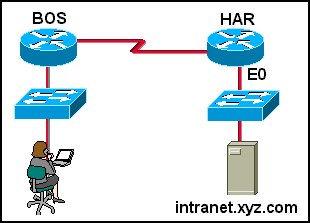
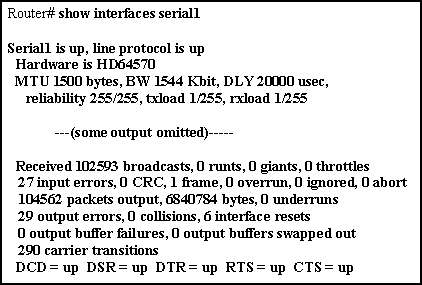
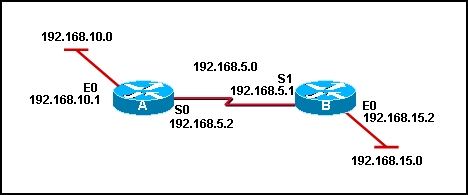
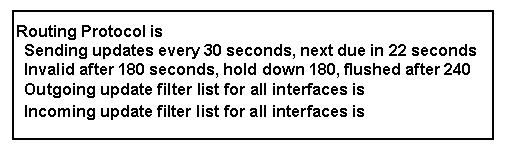
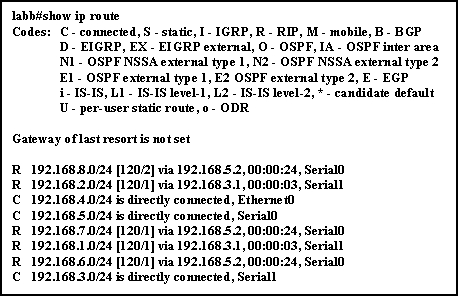
1 Tracing the route to Router_D (192.168.4.2) What can be concluded about the network shown in the graphic based on the output given? 2 Which of the following would be the default administrative distance of a static IP route that references the IP address of the next hop? 3 After issuing the show interfaces command, a technician notices the line "Serial1 is down, line protocol is down" in the output. Which of the following are possible reasons for this message output? (Choose three.) 5 9 The network administrator is using a PC to access a router via the router console port. Both the PC and the router are powered on and a cable has been connected between them. However, a session cannot be established. Which steps might fix this problem? (Choose two.) 10 Which command will display routing table information about all known networks and subnetworks? 14 16 Which items would be displayed when the show ip protocols command is executed? (Choose three.) 17 Which two are true regarding the debug commands? (Choose two.) 18 A network administrator suspects that a network is not being included in the routing updates. Which command will provide information on when the next update is due and which networks are advertised in the update? 21 Which of the following are advantages of using a static route? (Choose three.) 'study > ccna' 카테고리의 다른 글
[Schizo!, 2008. 10. 25. 14:50, study/ccna]
1 How does a source host use ICMP to confirm that a destination host is reachable? 2 Which type of message is generated by a host when the ping command is entered? 4 Which two statements are true regarding ICMP? (Choose two.) 5 How does ICMP improve data transfer reliability in IP networks? 6 Which layer protocols provide reliability for IP when needed? 7 Which devices along a data transmission path are notified by ICMP when delivery failures occur? 8 When a datagram is processed by a router on the path from source to destination, what happens to the value in the TTL field?" 9 Which condition could cause a fragmentation needed ICMP destination unreachable message to be sent? 10 11 Which three conditions must be met in order for host to host communication over an internetwork to occur on IP networks? (Choose three.) 'study > ccna' 카테고리의 다른 글
[Schizo!, 2008. 10. 25. 14:49, study/ccna]
1 Which command or set of commands will stop the RIP routing process? 3 Which of the following functions are performed by a router as routing information travels through the network? (Choose two.) 4 What do distance vector algorithms require each router in the network to send? 6 7 Which command will display RIP activity as it occurs on a router? 9 10 How would an administrator configure a static route for use if a primary route failed? 11 Which statements describe RIP? (Choose three.) 12 A router has routes to several subnets of a classful network in its routing table. A default route is defined on the router but the ip classless command is disabled. If the router receives packets for a subnet that is not in its routing table but is in the same classful network as the other subnets, what will happen to the packets? 13 15 Which statements describe load balancing when RIP is configured as the routing protocol? (Choose two.) 16 • RouterB(config)# router rip • RouterB(config)# router rip 18 When a routing table update is received by a router in a distance vector network, which of the following occurs? 20 When does RIP send routing table updates? (Choose two.) 21 Which of the following can exist in a distance vector network that has not converged? (Choose three.) 22 What happens to a static route entry in a routing table when the outgoing interface is not available? 'study > ccna' 카테고리의 다른 글
[Schizo!, 2008. 10. 11. 13:15, study/ccna]
1 Which command or set of commands will stop the RIP routing process? 3 Which of the following functions are performed by a router as routing information travels through the network? (Choose two.) 4 What do distance vector algorithms require each router in the network to send? 6 7 Which command will display RIP activity as it occurs on a router? 9 10 How would an administrator configure a static route for use if a primary route failed? 11 Which statements describe RIP? (Choose three.) 12 A router has routes to several subnets of a classful network in its routing table. A default route is defined on the router but the ip classless command is disabled. If the router receives packets for a subnet that is not in its routing table but is in the same classful network as the other subnets, what will happen to the packets? 13 15 Which statements describe load balancing when RIP is configured as the routing protocol? (Choose two.) 16 • RouterB(config)# router rip • RouterB(config)# router rip 18 When a routing table update is received by a router in a distance vector network, which of the following occurs? 20 When does RIP send routing table updates? (Choose two.) 21 Which of the following can exist in a distance vector network that has not converged? (Choose three.) 22 What happens to a static route entry in a routing table when the outgoing interface is not available? 'study > ccna' 카테고리의 다른 글
[Schizo!, 2008. 10. 11. 13:13, study/ccna]
1 What can be concluded about the routing process on a router if the commands router rip and network 192.5.5.0 have been issued? (Choose three.) 2 Which two protocols use an addressing scheme to direct user traffic? (Choose two.) 6 What is the purpose of a routing protocol? 8 How does a router learn about routes to a network? (Choose three.) 9 Which type of address does a router use to make routing decisions? 11 Select the statements that describe link-state routing processes? (Choose three.) 12 Why is it necessary to specify a list of networks when configuring an interior routing protocol? 13 15 Which category of routing algorithms discovers and maintains a topological map of the entire internetwork? 17 Which of the following statements are true regarding the command ip route 172.16.1.0 255.255.255.0 172.16.2.1? (Choose three.) 18 20 Given the command, RouterC(config)# ip route 197.5.2.0 255.255.255.0 192.10.1.1, what does the address 192.10.1.1 represent? 21 Which of the following conditions must be met in order for a network to have converged? 'study > ccna' 카테고리의 다른 글
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
정보처리산업기사 CCNA 2 - Module 11 Exam 크레이브 zn40 율량 스타크래프트2 티스토리초대 티스토리 초대장/ 티스토리초대 GTA4 하마치 김사랑 진중권 블로그 100분토론 디워 GTA4 치트 3.0 해킹 마재윤 모토로라zn40 데몬 최신버전 UK B-Boy Championships GTA4 치트키 티스토리 초대장 비보이
BLOG Total Visitors
Today Hit, Yesterday Hit 
|
|||||||||||||||||||||||||||||||||||||||||||||||||||