1 What can be concluded about the routing process on a router if the commands router rip and network 192.5.5.0 have been issued? (Choose three.)
• A distance vector routing protocol was used.
• A link-state routing protocol was used.
• Routing updates will broadcast every 30 seconds.
• Routing updates will broadcast every 90 seconds.
• Hop count is the metric used for route selection.
• Bandwidth, load, delay, and reliability are the metrics used for route selection.
2 Which two protocols use an addressing scheme to direct user traffic? (Choose two.)
• IP
• EIGRP
• IPX
• OSPF
• RIP
3 What are some of the advantages of using a link-state routing protocol instead of a distance vector routing protocol? (Choose two.)
• The topology database eliminates the need for a routing table.
• Frequent periodic updates are sent to minimize the number of incorrect routes in the topological database.
• Routers have direct knowledge of all links in the network and how they are connected.
• After the inital LSA flooding, they generally require less bandwidth to communicate changes in a topology.
• Link-state protocols require less router processor power than distance vector protocols.
4 If dynamic routing is not configured on a router, how do routing table updates occur?
• Link state advertisements are sent from other routers.
• Updates are made to the routing table by the administrator.
• Best path information is communicated by network hosts.
• The routing table is updated by neighboring routers.
5 Why is fast convergence desirable in networks that use dynamic routing protocols?
• Routers will not allow packets to be forwarded until the network has converged.
• Hosts are unable to access their gateway until the network has converged.
• Routers may make incorrect forwarding decisions until the network has converged.
• Routers will not allow configuration changes to be made until the network has converged.
6 What is the purpose of a routing protocol?
• It is used to build and maintain ARP tables.
• It provides a method for segmenting and reassembling data packets.
• It allows an administrator to devise an addressing scheme for the network.
• It allows a router to share information about known networks with other routers.
• It provides a procedure for encoding and decoding data into bits for packet forwarding.
7 Which are the primary functions used by a router when forwarding data?(Choose two.)
• data encryption
• error notification
• packet switching
• address identification
• path determination
• packet validation
8 How does a router learn about routes to a network? (Choose three.)
• Information is gathered from its own configuration regarding directly connected networks.
• Switches forward destination address information to each router.
• Hosts communicate destination network information to each router.
• Other routers forward information about known networks.
• Routes are entered manually by a network administrator.
• Routes are learned from information gathered from ARP tables.
9 Which type of address does a router use to make routing decisions?
• source IP address
• source MAC address
• destination IP address
• destination MAC address
10 Describe the switching function that occurs in a router.
• allows the router to make forwarding decisions based on Layer 2 addressing
• uses network addressing to select the best route and interface to forward data
• accepts a packet on one interface and forwards it to a second interface
• enables the router to select the most appropriate interface for forwarding a packet
11 Select the statements that describe link-state routing processes? (Choose three.)
• Each router develops its own map of the entire network.
• Routers send triggered updates when changes in the network occur.
• Link-state routing protocols place a higher load on router resources during the routing protocol initialization.
• Link-state protocols are more prone to routing loops than distance vector routing protocols.
• Networks using link-state routing protocols are slower to reach convergence after changes have occurred than those using distance vector protocols.
12 Why is it necessary to specify a list of networks when configuring an interior routing protocol?
• to tell the router how to reach those networks
• to tell the router which attached networks participate in routing updates
• to tell the router which set of metrics to use for the attached networks
• to tell the router which routing protocol to use
13

Assuming that the network shown in the graphic is converged and dynamic routing is enabled, which of the following conditions will cause a modification to the Orlando routing table? (Choose two.)
• The device connecting the S0 interface of the Tampa router to the serial link loses power.
• A network administrator shuts down the Orlando router E0 interface.
• A DCHP server connected to the Tampa E1 network loses power.
• The IP address of a workstation on the Orlando E0 network is reassigned.
• A host on the Orlando E1 network transmits data to a server on the Tampa E1 network.
• A Telnet connection to the Orlando router fails.
14 All routers at a medium sized company have been upgraded. During the upgrade, the network administrator determined that a more advanced routing protocol using a combination of both distance vector and link state features should be implemented. Which protocol should be selected?
• RIP
• BGP
• OSPF
• EIGRP
15 Which category of routing algorithms discovers and maintains a topological map of the entire internetwork?
• static
• Bellman-Ford
• exterior gateway
• Internetwork Packet Exchange
• distance vector
• link-state
16 Which is an exterior routing protocol commonly used between ISPs?
• RIP
• BGP
• OSPF
• EIGRP
17 Which of the following statements are true regarding the command ip route 172.16.1.0 255.255.255.0 172.16.2.1? (Choose three.)
• This command is used to set up a static route.
• This command is used to set up a default route.
• This command is entered from global configuration mode.
• All packets intended for network 172.16.1.0 will be sent to gateway 172.16.2.1.
• All packets intended for network 172.16.2.1 will be sent to gateway 172.16.1.0.
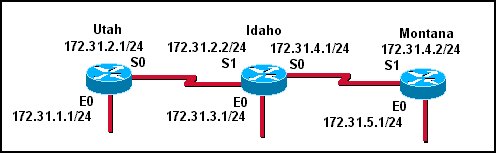
18
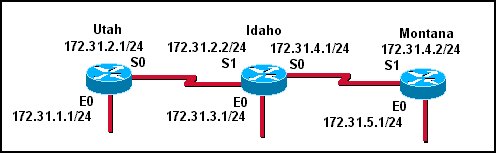
Referring to the diagram, which commands will enable hosts on the Idaho E0 network to reach hosts on the E0 network of the Montana router? (Choose two.)
• Montana(config)# ip route 172.31.5.0 255.255.255.0 172.31.5.1
• Montana(config)# ip route 172.31.3.0 255.255.255.0 172.31.4.1
• Idaho(config)# ip route 172.31.5.0 255.255.255.0 172.31.4.1
• Idaho(config)# ip route 172.31.5.0 255.255.255.0 172.31.4.2
• Idaho(config)# ip route 172.31.5.1 255.255.255.0 172.31.4.1
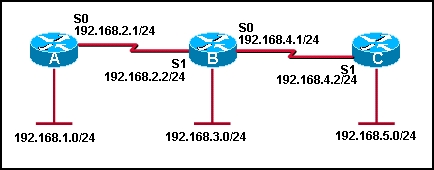
19
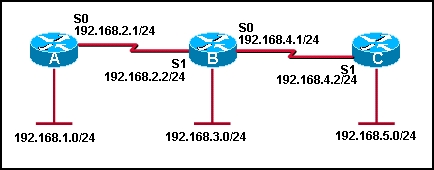
Which of the following are valid static IP routes? (Choose three.)
• RouterB(config)# ip route 192.168.5.0 255.255.255.0 S1
• RouterC(config)# ip route 192.168.1.0 255.255.255.0 S1
• RouterA(config)# ip route 192.168.3.0 255.255.255.0 192.168.2.2
• RouterB(config)# ip route 192.168.1.0 255.255.255.0 192.168.2.2
• RouterC(config)# ip route 192.168.2.0 255.255.255.0 192.168.4.1
• RouterA(config)# ip route 192.168.4.0 255.255.255.0 192.168.2.1
20 Given the command, RouterC(config)# ip route 197.5.2.0 255.255.255.0 192.10.1.1, what does the address 192.10.1.1 represent?
• the source host
• the next hop router
• the outbound interface
• the destination network
21 Which of the following conditions must be met in order for a network to have converged?
• The routers in the network are operating with dynamic routing protocols.
• The routers in the network are operating with compatible versions of IOS.
• The routers in the network are operating with the same routing tables.
• The routers in the network are operating with consistent routing knowledge.
22 Which two statements describe autonomous systems? (Choose two.)
• Interior gateway protocols are used between autonomous systems.
• Exterior gateway protocols are used between autonomous systems.
• An autonomous system may be under the control of multiple organizations.
• An autonomous system is identified by a 16 bit number assigned by ARIN.
• The autonomous system is identified in the network portion of the IP address.